Productivity can be challenging to track, no matter where employees are working. How do you know they’re using their tools as effectively as possible? How can you enable them to adopt best practices?
These are questions that managers often ask themselves. If they’re looking at the wrong things, it can get in the way of empowering their team. For example, you can’t grade productivity simply by “clock in/clock out” times.
In today’s hybrid and mobile offices, the value and work product an employee brings is a better gauge. But you also must look at what may be getting in the way of great employees doing great work.
Technology tools can slow down dedicated workers if they’re not familiar with them. Employees may be doing things the way they always have been, and not realize there is a better way. A faster way.
But productivity can be a tricky area to address. You don’t want to invade a remote employee’s privacy by tracking their every keystroke. Nor would that likely help with positive forward motion.
What’s the answer?
If your company uses Microsoft 365 then you have a tool you can use to find nuggets of productivity gold. This tool is Microsoft Productivity Score.
What Does Microsoft Productivity Score Do?
Microsoft Productivity Score looks at some core areas of your employees’ workflow. It also looks at them in aggregate. Because it’s looking at your team as a whole, you avoid issues with employees feeling personally spied on.
The tool gives you helpful insights that you can share with your staff. These insights help to boost their performance. It also includes hardware-related information. You can use this to see if your company tools are holding people back.
MS Productivity Score looks at the following areas.
People Experiences
This category looks at how people work. Are they using best practices for collaboration or are they doing things the hard way? Do meetings go on forever? Are employees still emailing attachments instead of using shared cloud storage links?
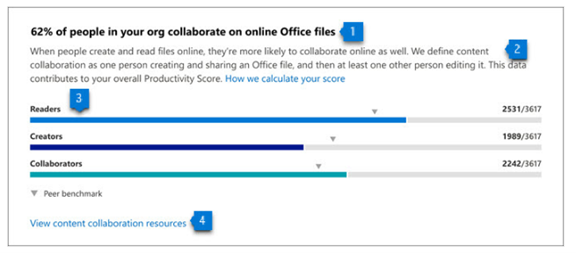
One example of an insight from this category is as follows. Each employee can save an average of 100 minutes per week by collaborating with online files. Productivity Score can show you where your team stands in this metric, and many others.
Saving 100 minutes per week is equal to approximately 86.6 hours per year. That’s over 2 full workweeks!
The subcategories within people experiences are:
- Communication
- Content collaboration
- Mobility
- Meetings
- Teamwork
Technology Experiences
Technology experiences look at the health and performance of your devices. Do you have hardware and software on endpoints that are causing issues? Is it slowing your team down? Are there network connectivity problems? Are apps updated as they should be?
This category will look at the technology that your team works with and let you know of any risk areas. When technology is not functioning well or isn’t secure, it can slow your business down.
You’ll find these three subcategories in the technology experiences area:
- Endpoint analytics (You need Intune for these)
- Network connectivity
- Microsoft 365 apps health
Special Reports
Besides the people and technology experiences, there is more. Microsoft Productivity Score has a special reports area. It provides details on business continuity.
This report can show you how employee collaboration and other activities are changing. It looks at these as your company goes through transitions. Such as when you transition to remote working or back to in-office work. This report tells you how these changes impact your team’s productivity.
How Productivity Score Helps Your Company
Automatic Metrics Tracking
Microsoft Productivity Score tracks your team’s use of Microsoft 365 applications automatically. It then will provide you with helpful information on how staff use their digital tools.
These metrics give you a good picture of whether employees are using best practices. Often, they simply need guidance to learn a more efficient way of doing something.
Insights to Understand the Data
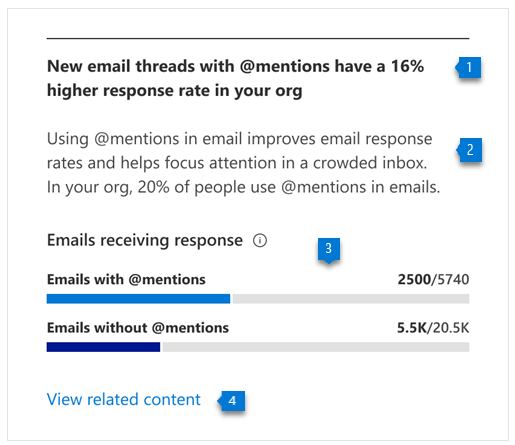
The tool provides you with helpful insights to understand the data. You won’t only get the metrics; you’ll get the context. This allows you to educate yourself. Then you can educate your employees on things that improve workflow and save time.
For example, getting a response quickly to a question saves time. But you may not realize that using @mentions can help achieve that. Productivity Score will tell you how many people use @mentions in team communications. And also, how much this increases the response rate.
Recommended Actions to Take
The third piece of guidance you gain is what to do about the information. Productivity Score will give you actionable recommendations to improve a metric. This helps you to improve productivity.
The combination of the metric, insight, and recommendation make this a comprehensive tool.
Would You Like to Get Started with Microsoft Productivity Score?
We can help you get your organization started with this great tool. And provide solutions to increase company productivity. Give us a call and let’s chat!
This Article has been Republished with Permission from The Technology Press.